
ED Arrests Punjab Minister Sanjeev Arora In Rs 100 Crore Money Laundering Case
The Enforcement Directorate (ED) on Saturday arrested Punjab minister Sanjeev Arora in connection with an ongoing Rs 100 crore money laundering investigation linked to alleged fraudulent Goods and Services Tax (GST) transactions, officials said.
Arora’s arrest came after a day-long search operation carried out across multiple locations associated with him and his business entities. The raids were conducted under the provisions of the Prevention of Money Laundering Act (PMLA), 2002.
According to officials, ED teams initiated coordinated searches early on Saturday at five premises spread across Delhi, Gurugram and Chandigarh. Of these, four locations were directly linked to Arora and his associated entities, while one office premises belonged to Hampton Sky Realty Limited, which is also under the agency’s scanner in the case.
Meanwhile, AAP MP Sanjay Singh reacted strongly to the arrest of Punjab Cabinet Minister Sanjeev Arora and alleged misuse of central investigative agencies in opposition-ruled states ahead of elections.
Speaking to ANI, Singh said, “ED is acting like a contract killer. State after state, raids are being done on rivals and they are being jailed. This has become the trend of ED. Their experiment in other states is being replicated in Punjab by PM Modi, ahead of elections. Today, cabinet minister Sanjeev Arora has been arrested. Nothing was found from Sanjeev Arora in three raids. Despite that, he has been arrested because this is the election model of the BJP. I would like to tell PM Modi, that his Aurangzeb-like policy will not work in Punjab…”
The investigation pertains to an alleged large-scale money laundering network involving fake GST transactions.
ED officials claim that Arora, through his company, generated fraudulent purchase invoices for mobile phones worth over Rs 100 crore from non-existent firms based in Delhi. These transactions were allegedly used to claim undue input tax credit (ITC), along with wrongful GST refunds on export credits and duty drawbacks.
Sources in the agency indicated that the alleged scheme enabled the accused to siphon off government funds by exploiting loopholes in the GST framework.
The ED further suspects that the proceeds of crime were routed through export channels and subsequently round-tripped back into India from Dubai in an attempt to legitimise the illicit gains.
Officials said the alleged activities caused substantial losses to the government exchequer and pointed to a well-organised financial trail involving shell entities and layered transactions.
Search operations were still underway at multiple premises linked to Arora and his associates in Chandigarh and the Delhi-NCR region at the time of filing this report. These include his official residence allotted to him as a minister.
The ED is expected to produce Arora before a special PMLA court and seek custodial interrogation to further probe the financial trail and identify other individuals involved in the case. (ANI)
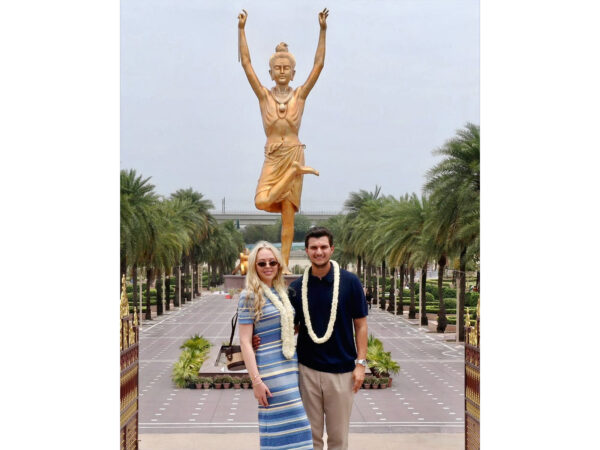
Tiffany Trump And Her Husband On India Tour, Visit Akshardham Temple In Delhi

‘All Three Services Preparing Well For Operation Sindoor 2.0, If It Takes Place’: Chief of Army Staff
Abhishek Agarwal Urges CM Suvendu Adhikari To Back ‘The Bengal Files’ Release In West Bengal
